Part 5 - How To Secure Distributed Applications with KEYCLOAK - Spring Security Keycloak Adapter - YouTube
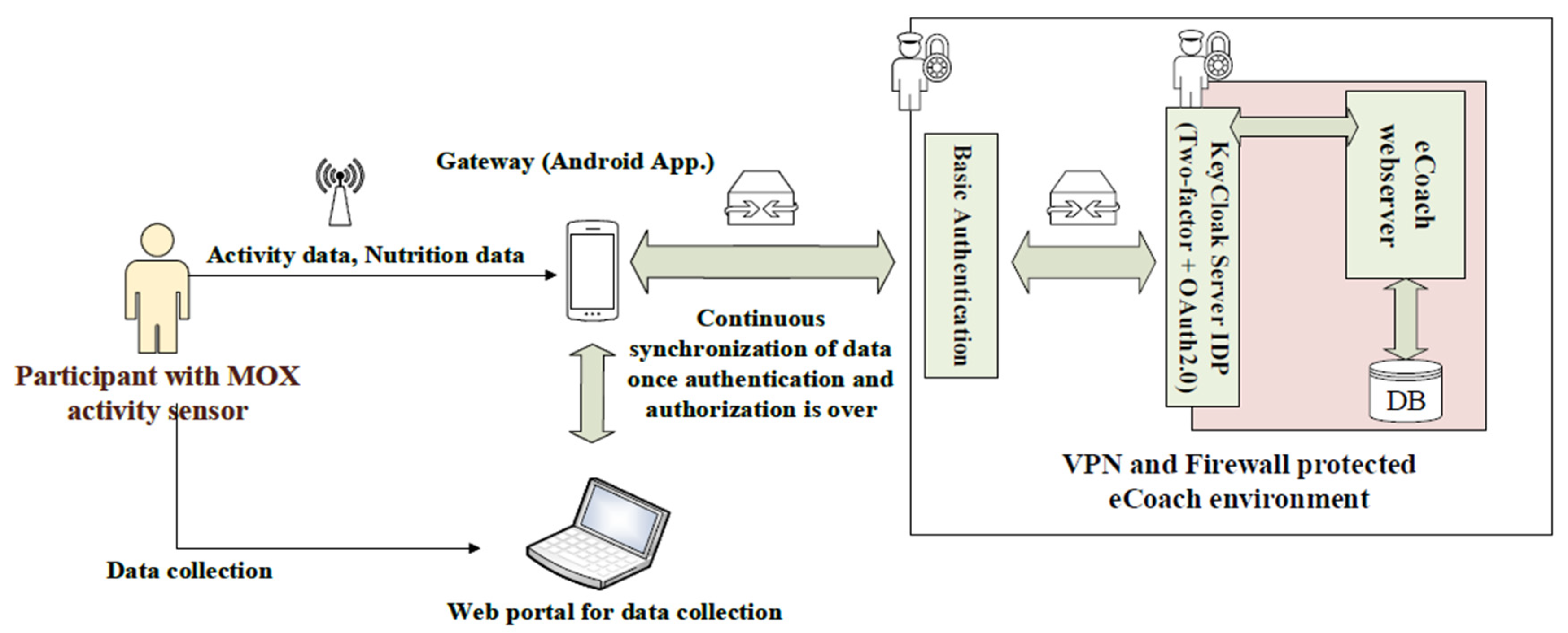
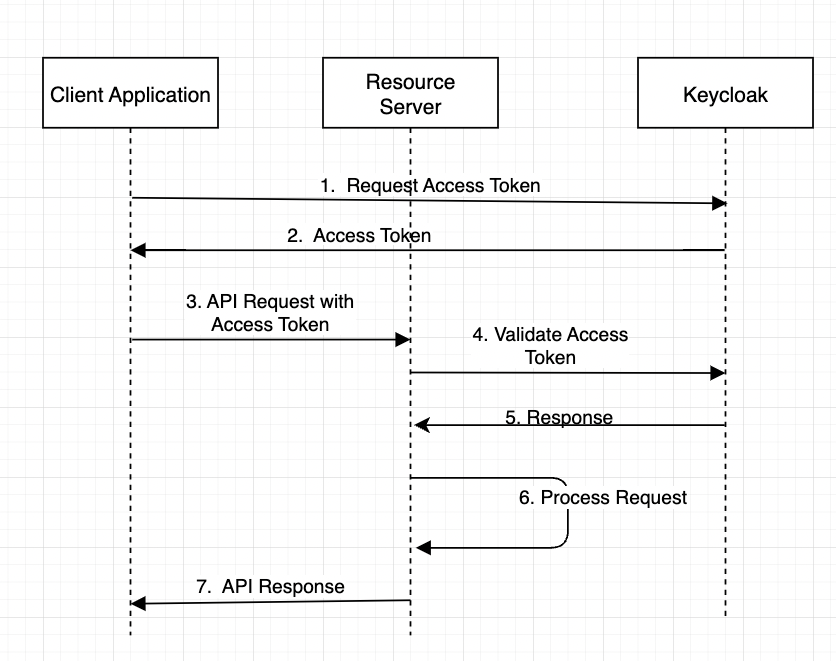
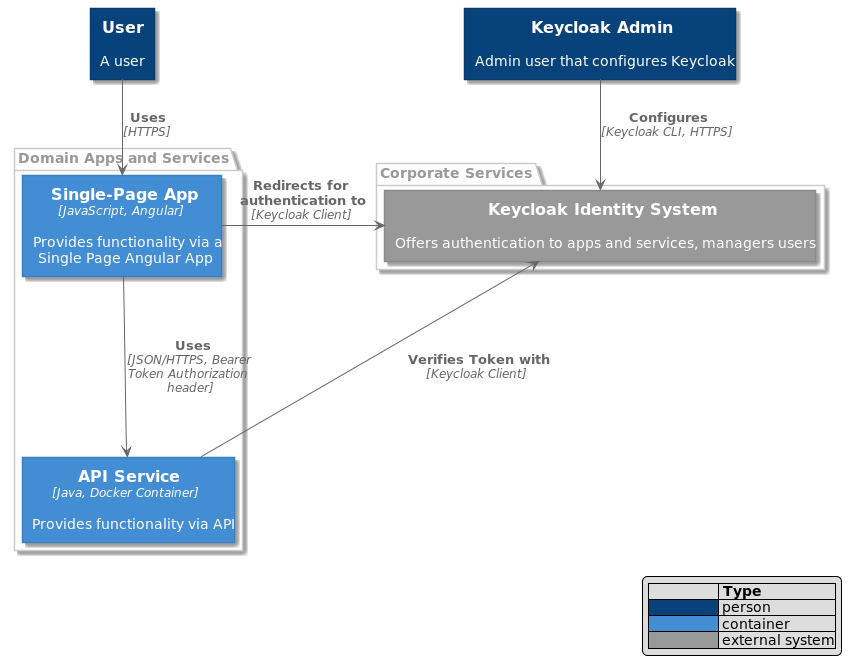
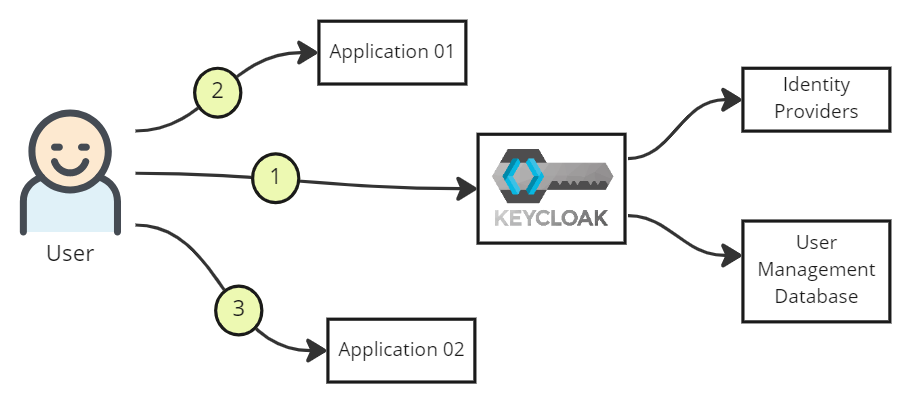
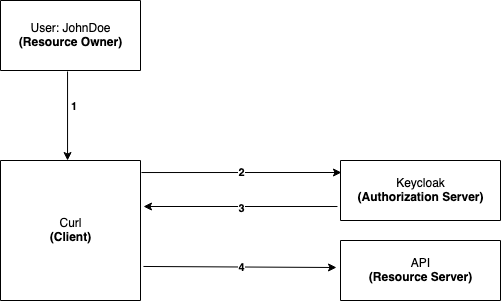
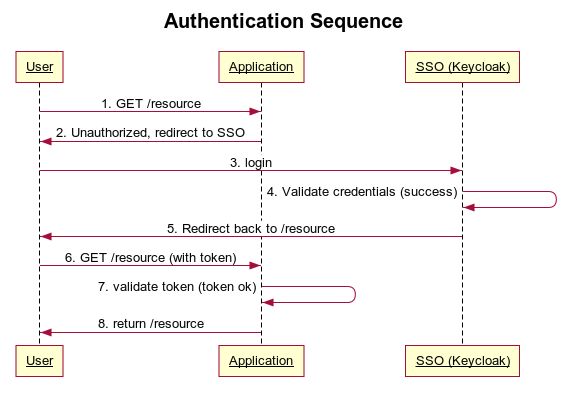
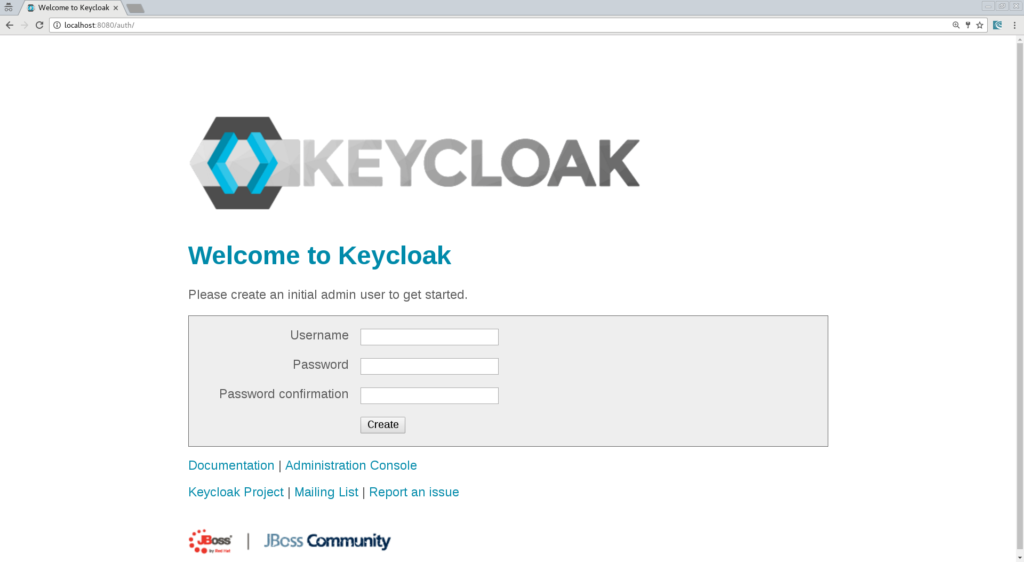
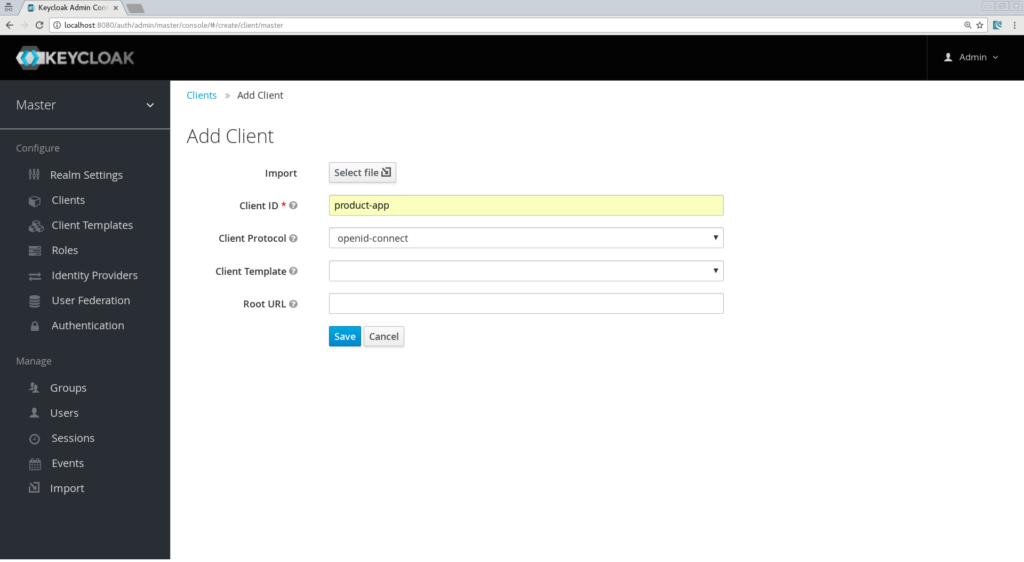
Sensors | Free Full-Text | Applying Spring Security Framework with KeyCloak-Based OAuth2 to Protect Microservice Architecture APIs: A Case Study
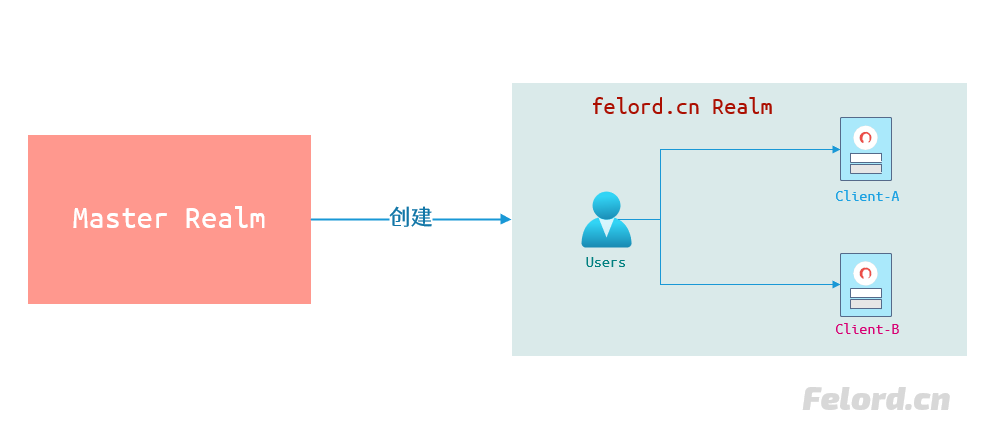
Protecting Your Spring Boot Applications with the Keycloak Authentication Authorization Platform - Spring Cloud